Documentation Index
Fetch the complete documentation index at: https://docs.spacebaseapp.com/llms.txt
Use this file to discover all available pages before exploring further.
SOC 1 Type II Report and Internal Controls
Spacebase maintains a strong focus on security, data protection, and operational controls to support enterprise accounting and lease management workflows. The platform is designed with modern cloud-based security practices, including controlled system access, authentication protocols, and secure data management processes to help protect customer information and maintain system reliability. Spacebase undergoes independent SOC 1 Type II compliance reporting, providing customers and prospects with additional assurance regarding the design and operation of their security controls and processes. Customers and prospective customers may request a copy of Spacebase’s SOC 1 Type II report directly from the Spacebase team as part of their security and vendor review process.Approval Workflows & User Activity Logging
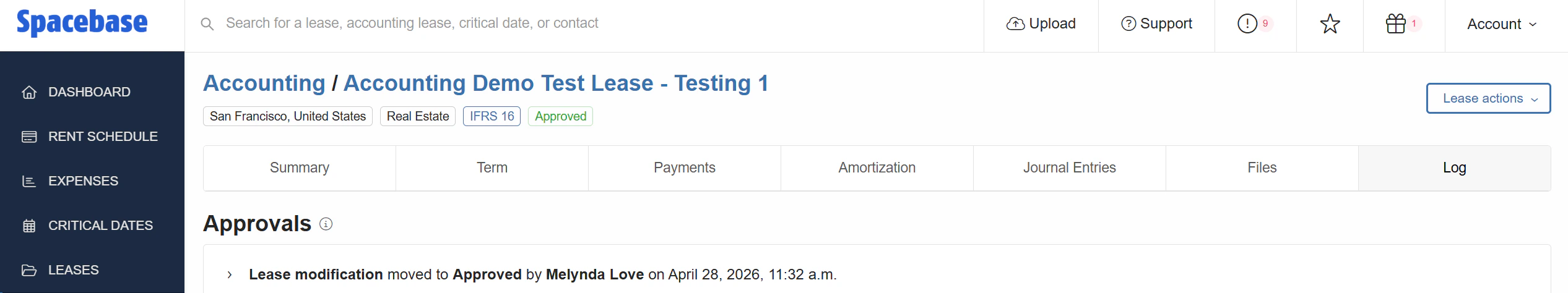
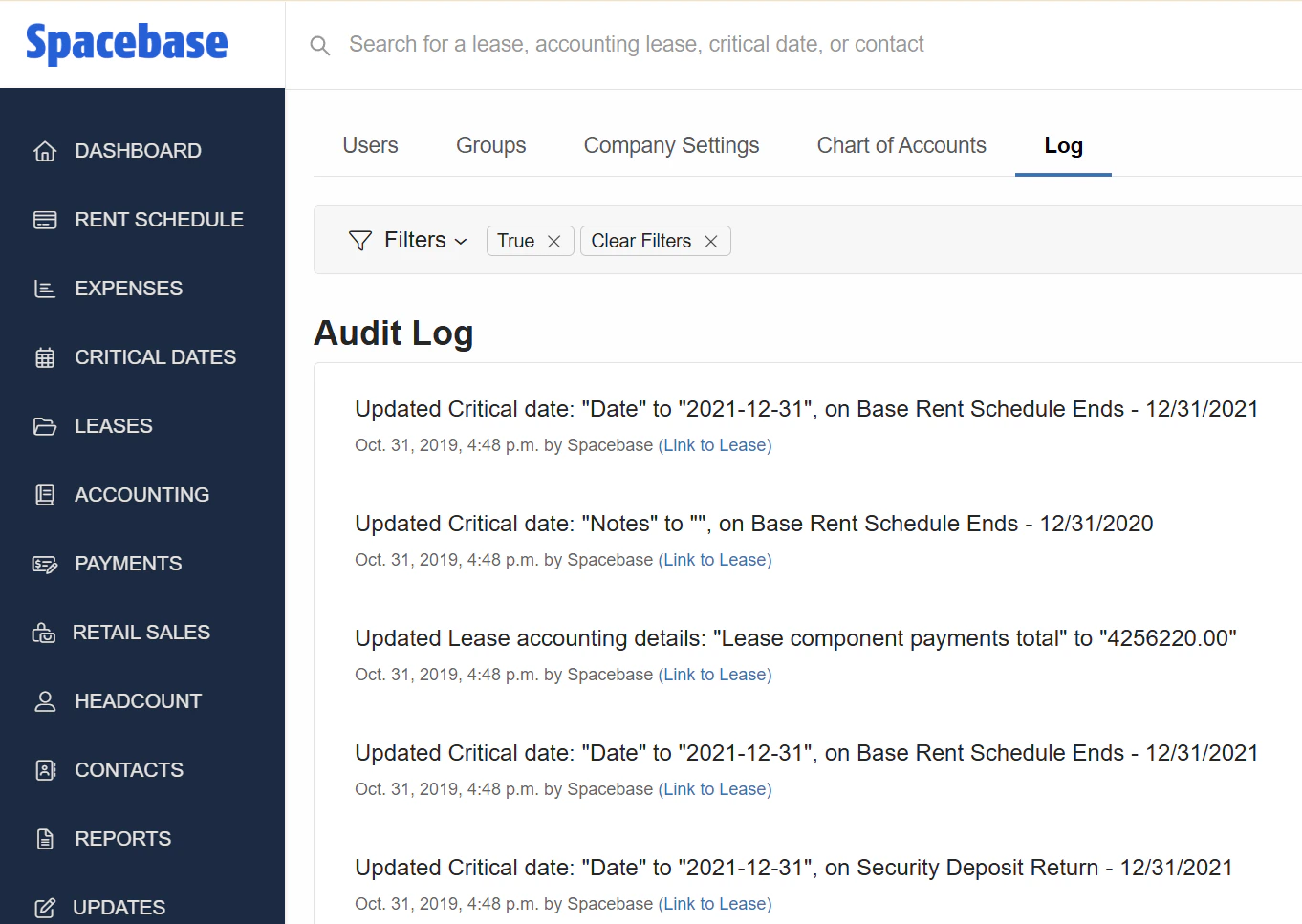
Spacebase includes configurable approval workflows designed to support strong internal controls, governance, and review processes across lease accounting and operational activities. Organizations can establish approval requirements for key workflows and data changes, helping ensure that transactions, lease updates, and other critical activities are reviewed and authorized by appropriate personnel before being finalized.